What is Sodinokibi (REvil) ransomware?
First identified in 2019, Sodinokibi (also known as REvil or Ransomware Evil) was developed as a private ransomware-as-a-service (RaaS) operation, thought to be based in Russia. The wide reach and efficiency of Sodinokibi was seen almost immediately, as it became the fourth most common type of ransomware within its first four months.
The RaaS approach to distribution means that many people have had access to the ransomware’s code, resulting in a wide range of variants and increasingly aggressive attacks from different vectors, including spam and server attacks. This makes it a particularly dangerous form of ransomware.
This article looks at the origins of Sodinokibi, how it operates, and what can be done to secure your network against it.
Try the Avast Business Hub FREE for 30 days
All businesses deserve best-in-class cybersecurity. Download the Avast Business Hub and try it for 30 days, risk-free.
What is Sodinokibi/REvil ransomware?
Sodinokibi is provided in a ransomware-as-a-service (RaaS) format, meaning that affiliates are used to distribute the ransomware, and developers and affiliates split the money made through ransom payments. It shares similarities with the known code from notorious hacking groups DarkSide and GandCrab, which is thought to be behind as much as 40% of ransomware infections worldwide.
The virus is typically delivered through phishing techniques, tricking users into opening malicious files disguised as email attachments, documents, and spreadsheets.
The focus of this type of malware is high-profile ransomware attacks against large organizations and public figures, with the intention of both securing large ransom payments and publishing private information on the group’s own blog. Sodinokibi has been used by cybercriminals to:
- Steal around 1TB of data from celebrity law firm Grubman Shire Meiselas & Sacks, whose clients include Madonna and Lady Gaga, in May 2020
- Attempt to extort Apple using stolen product schematics in April 2021.
- Attack US tech contractor HX5 in July 2021. This resulted in US President Joe Biden pressuring Vladimir Putin before taking action against the group and is the most high-profile Sodinokibi attack to date.
Who is behind Sodinokibi ransomware?
The origin of the ransomware’s creators has been hard to identify. Initially, attacks seemed to focus on Asia, but they soon emerged in Europe. One region that was not attacked was Russia, suggesting that this is where the malware originated from.
An operation involving 17 countries resulted in five suspects connected to Soninokibi/REvil being arrested. In January 2022, Russian authorities announced that the group had been dismantled.
While this is positive news, it does not mean that the threat is over. Due to the ransomware’s style of distribution and the creator’s relationship with other groups, Sodinokibi code could still be used or modified to target new attack vectors.

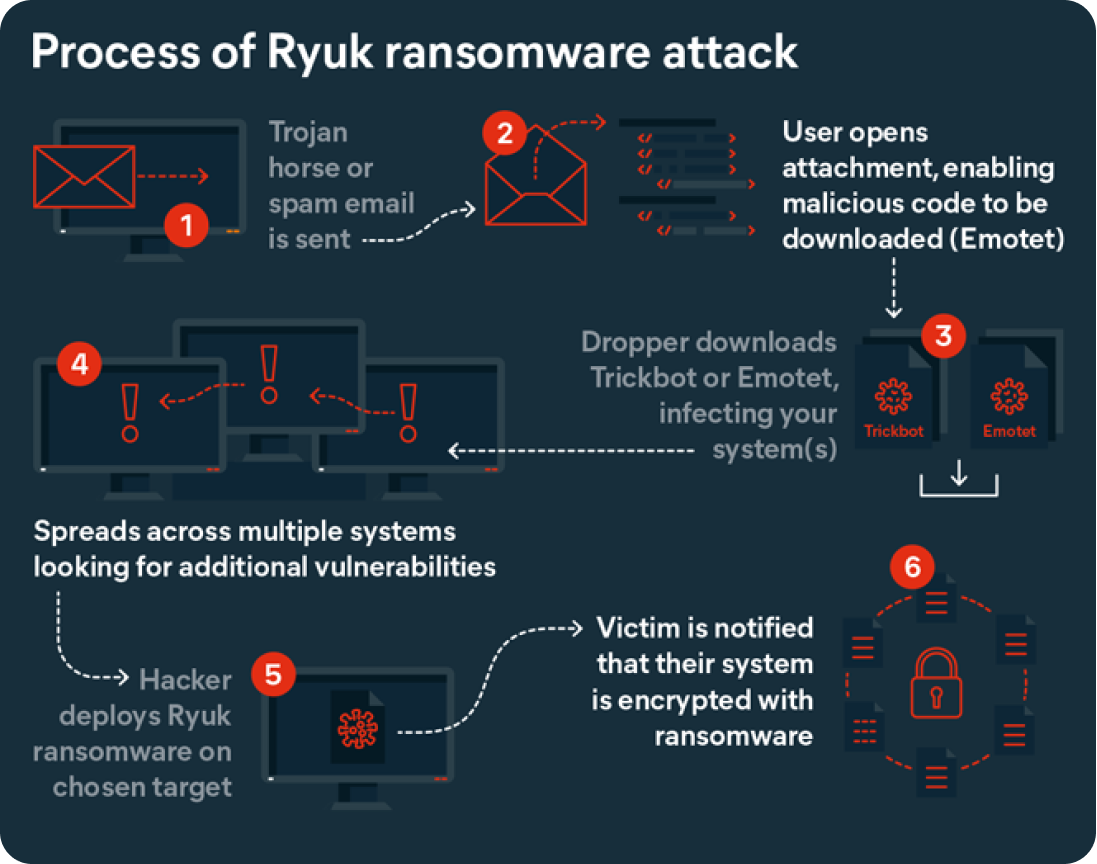
How does Sodinokibi ransomware work?
One of the main challenges with Sodinokibi ransomware is detecting it. Much of its code is disguised or encrypted, making it difficult for antivirus scanners to identify – highlighting the importance of establishing a multi-layered, holistic security strategy that combines training, best practices, and software to identify potential threats as early as possible.
This section will look closely at the attack process to help users to better understand how the ransomware operates.
For more information about other high-profile ransomware types, read our guides to Phobos and WannaCry.
1. Initializing the ransomware
An attack begins by ensuring it is the only process running on the target endpoint. It then runs exploits to identify vulnerabilities caused by the failure to install security patches. Once this has been done, the next step is to change its access permissions to gain full admin privileges. It will then restart in Admin mode.
The system is then scanned for language IDs. An exemption list is included in the code, identifying countries by device language so the ransomware does not attack endpoints in eastern European countries. This information helped investigators identify that the hacker’s group was operating from Russia.
Next, files in the Windows backup system (Shadow Copies) are deleted and the boot policy editor is used to disable recovery modes. The system is then scanned for backup folders, which are deleted and overwritten to make them impossible to recover.

2. Key generation and exchange
Encryption keys are created in pairs – one publicly available, the other held by the attacker. Without both keys, recovering the stolen data is almost impossible. Sodinokibi uses a key generation and exchange algorithm known as an Elliptic-curve Diffie-Hellman (ECDH).

3. Encryption
Sodinokibi uses two types of encryption:
- AES is used to encrypt the private key and for data transfer across networks.
- Salsa20 is used for encrypting user files.
The user’s documents are collected from all files that have not been marked exempt and encrypted with Salsa20, generating a unique key for each file. It will be clear which files have been encrypted as the ransomware adds a file extension to each affected file.
The operation will now prepare the data for delivery to the attacker’s server.
4. Demands
After a file has been encrypted, a ransom note is created and placed in the same folder. This process is repeated for every folder containing encrypted files. A template for this is included in the Sodinokibi ransomware and is automatically updated with the user’s ID and other relevant information, including a key.

Sodinokibi decryption
The ransom note provides clear instructions for how the users can recover their data. This includes installing a TOR browser, visiting a unique link and entering a key.
It is on this page that the details of the ransom are presented. Users must pay to download decryption software and are given a deadline to do so. Failure to meet the deadline results in the price doubling. Payment is demanded in Bitcoin.

In September 2021, it was announced that cybersecurity firms and law enforcement in the US had created a free, universal decryptor key that could return files to any companies that were attacked prior to July 13th, 2021. However, to protect your business data against further attacks, a ransomware protection tool is crucial, as the key is not guaranteed to work on encryptions that take place after this date.

Protection against a REvil attack
As such a varied and dangerous form of ransomware, business users must ensure that their network and devices are protected against the threat of a Sodinokibi/REvil ransomware attack. Essential steps to take include:
- Regularly updating systems. Vulnerabilities are a common route into systems, making it essential that patches, fixes, and updates are applied as soon as they become available.
- Backing up data. As the name suggests, ransomware attacks are designed to steal data and sell it back to the owners. Keeping secure, remote backups means that vital data and documents will remain secure and accessible, even if the worst should happen.
- Controlling who has access. Access permissions should be strictly limited to those who need direct access. Audit company-wide permissions to ensure that admin privileges are kept to a minimum, reducing access to network controls should a user account be breached.
- Adopt security best practices. Another way to protect business data is to ensure that security best practices are implemented. This should include a requirement for strong passwords, a process for flagging suspicious activity, and remote working agreements to ensure devices are updated and secure. As part of this, ransomware protection software and malware scanners should be in place across all endpoints connected to the business network to help detect and remove ransomware.
- Conduct regular inspections and vulnerability assessments. Event logs should be checked on a regular basis so that unusual activity, such as high activity outside business hours, can be quickly spotted and assessed.
- Have a response plan. Disaster planning is key for business protection – and that extends to the digital world. Ensure that attack drills are held regularly, that staff know who to contact in the event of a ransomware attack, and that a business continuity plan (BCP) is in place so the business can continue to operate following an attack
Protect against Sodinokibi ransomware
Members of the group behind the Sodinokibi/REvil ransomware may have been apprehended in January 2022, but their malware is just one of many. Protect your company from a broad range of attacks with the Avast Business Hub, our integrated, cloud-based security platform for SMBs.